CAA = Certification Authority Authorization
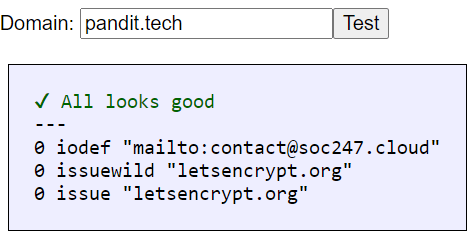
Here is an example:
Simple but effective protection against rogue Certificate Authorities.
You will need two or three DNS records. As shown in example below.
First Record
- Type: CAA
- Name: pandit.tech #Use your domain
- Tag: issue / Only allow specific hostnames
- CA domain name: letsencrypt.org
Second Record
- Type: CAA
- Name: pandit.tech #Use your domain
- Tag: issuewild / Only allow wildcards
- CA domain name: letsencrypt.org
Third Record
- Type: CAA
- Name: pandit.tech #Use your domain
- Tag: iodef / Send violation reports to url
- Value: contact@youremail.com
Notes
- Please use either issue or issuewild.
- Some DNS service providers add their own CAA records without informing you. Be on the alert.
- Please set up CT Monitor (Certificate Transparency Monitor), so that you get an alert if criminals issue certificates for your domains.
How to measure success?
You can use CAA checker at CAAtest.co.uk or similar tools.
I suggest you also monitor Certificates issued for all of your domain names. This is known as Certificate Transparency monitoring.
We use a strictly necessary technical cookie (__Host-PHPSESSID) to ensure secure browsing. No consent is required under GDPR. See our Cookie Policy and Privacy Policy for details.